
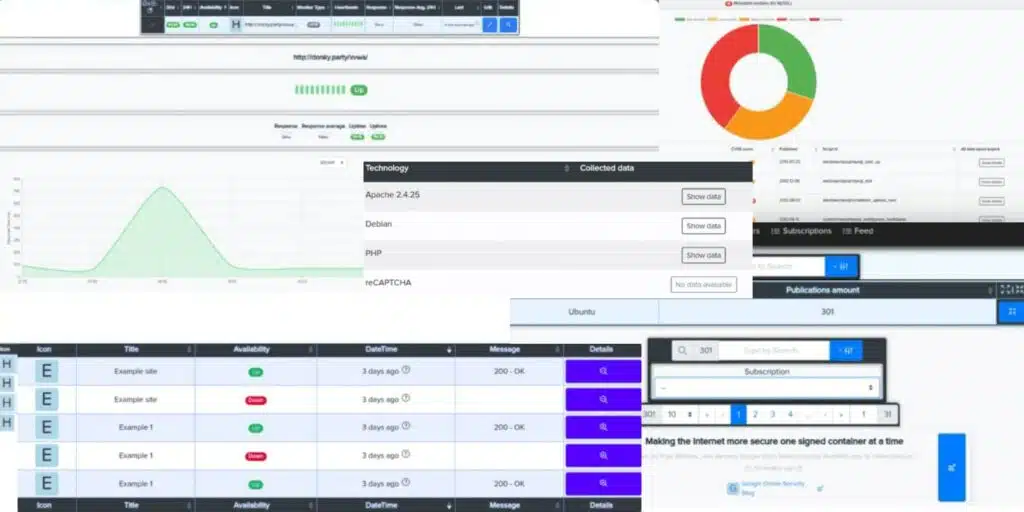
Cryeye – Multi-slide safety monitoring
Services

Scanning web vulnerabilities
Get combined security scan results using various audit tools.

Infrastructure Infrastructure scanning
Start a round-the-clock security scan of your infrastructure for vulnerabilities and incorrect configurations.

Mobile Application Mobile application scanning
The deepest and most advanced scanning of Android and iOS mobile apps. Detection of all possible vulnerabilities and leaks in your mobile applications.

Smart Contract and Repository Scanning of smart contracts and repositories
Constantly scan and identify potential problems in your smart contracts and your organization's source code repositories.

Web and DarkNet recon Intelligence and monitoring on the Web and DarkNet
Get audit results on request and continuously monitor the Web and DarkNet for vulnerabilities and leaks of your confidential data. When your data is stolen, you will find out about it faster than the thief will have time to sell it. When you have a zero-day vulnerability, you will know about it faster than a hacker will have time to use it.
Reports, support and integration
Together with our partner, the CQR team, we provide full support for our solution. Our security analysts, pentesters, developers, project managers and account managers will help you. Cryeye is a very flexible solution, so we can add new customized features or reports to meet any of your specific requirements.
The Cry eye solution can be used not only as an independent service, but also integrated into your SaaS systems or solutions that perform any type of audit or monitoring, analysis or verification of sites, applications, source code or personal data of your users. We will help you add to your services the unique functionality necessary to stay ahead of the competition.
| Competitors | Cryeye | Acunetix | Netsparker | Metasploit |
| Cloud Application | + | + | – | – |
| OSINT and Domain profiling | + | – | – | +/- |
| Detection of blacklisting and filters | + | – | – | + |
| Dork-search for vulnerabilities and domains | + | – | – | – |
| Using external services: Shodan, ZoomEye, Leak-Lookup, etc. | + | – | – | – |
| GitHub Analysis | + | – | – | – |
| Analysis in the “white box” mode | + | – | – | – |
| Ability to request hotfixes for web applications | + | – | – | – |
Features of the solution
- Automatic inventory of all detected technologies.
- Constant monitoring of exploits, including zero-day exploits.
- Automatic code security analysis of all popular programming languages: PHP, Java, Golang, Python, C/C++, Ruby, etc. Manual code security analysis on request.
- CI/CD and virtualization support: Terraform, Docker image security verification, Azure Resource Manager, etc. Performing your DevOps and Security DevOps tasks manually by our specialists.
- Audit and monitoring of Active Directory security using agent software.
- Audit of smart contracts with three levels of testing. Security features for the most popular blockchains: Ethereum, Polygon, Solana, Near, Heco, XDC. Manual audit of smart contracts from our experts.
- The world's best functionality for monitoring email, Github, the range of your IP addresses and your trademark on the Web and DarkNet for leaks and zero-day vulnerabilities. Threat intelligence.
- Automatic verification of findings for the formation of facts.
- All management and all reports are right in your browser.
- Quick access to large amounts of data due to efficient structuring and modern interface elements.
- A master based on artificial intelligence helps to communicate with the system without the need for a deep understanding of technology.
- Managing facts using the status system.
