
Security Center (SOC) as a service
Subscription to the permanent protection of the entire company
Business security is a complex of activities with many dynamic elements. H-X combines all these elements for you. Security Operations Center (SOC) as a service, it is a profitable alternative to investing in the implementation and maintenance of your own SOC.
Business security is a complex of activities with many dynamic elements. H-X combines all these elements for you. Security Operations Center (SOC) as a service, it is a profitable alternative to investing in the implementation and maintenance of your own SOC.
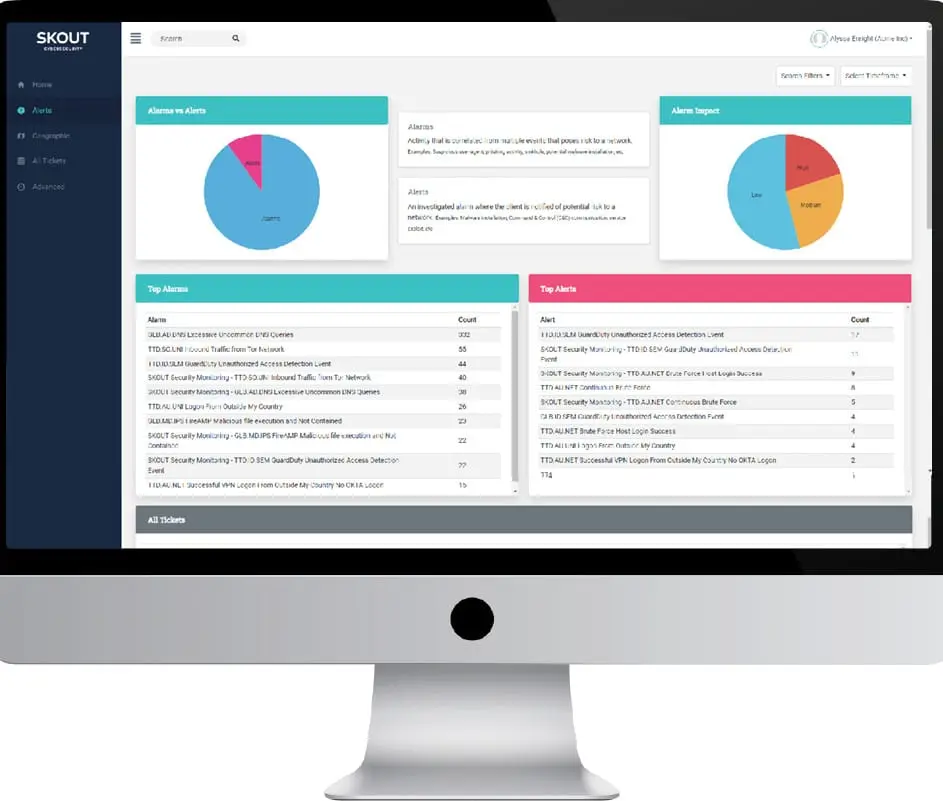
H-X provides a SOC (SOC as a Service, Saas) service using Splunk and FortiSIEM platforms. It is a managed solution that collects, combines and normalizes log data from hundreds of sources for analysis using artificial intelligence, an analytical platform, threat analytics, SIEM and a 24-hour security management center. This solution identifies threats such as, for example, incorrect login events, coordinated attacks, multi-factor bypass and fraudulent agents.
The "Three pillars” of our SOC
Technologies: event log management, security event management, incident management, security management automation and response, user behavior analytics and machine learning, threat detection, orchestration, etc.
Processes: technological, business processes, analytical, operational, communication, etc.
People: IT specialists and security engineers, security analysts, incident response team, etc.
The "Three pillars” of our SOC
Technologies: event log management, security event management, incident management, security management automation and response, user behavior analytics and machine learning, threat detection, orchestration, etc.
Processes: technological, business processes, analytical, operational, communication, etc.
People: IT specialists and security engineers, security analysts, incident response team, etc.

Technological capabilities
- Event Log Management Platforms
- User Behavior and Entity Analysis
- Machine learning
- Coordination and response
- Digital Forensics
- Distributed cloud platform with high availability architecture, etc.
- Our capabilities include monitoring of the most popular server platforms, network technologies, applications, databases, virtualization platforms, storage, backup, cloud platforms, etc.
SOC Levels
Level 1 – Alert analysts continuously monitor alert queues; sort security alerts; monitor the health of security sensors and endpoints; collect data and context necessary to get started with Level 2.
Level 2 – Incident response specialists conduct in-depth analysis of incidents, comparing data from various sources; determine whether a critical system or dataset has been affected; advise on troubleshooting; provide support for new analytical methods for detecting threats.
Level 3 – Domain experts and threat hunters have in-depth knowledge of networks, endpoints, threat analysis, forensic analysis and malware decompilation, as well as check the functioning of specific applications or the underlying IT infrastructure; act as "incident hunters" without waiting for them to appear; actively participate in the development of, configuring and implementing threat detection analytics.
Level 2 – Incident response specialists conduct in-depth analysis of incidents, comparing data from various sources; determine whether a critical system or dataset has been affected; advise on troubleshooting; provide support for new analytical methods for detecting threats.
Level 3 – Domain experts and threat hunters have in-depth knowledge of networks, endpoints, threat analysis, forensic analysis and malware decompilation, as well as check the functioning of specific applications or the underlying IT infrastructure; act as "incident hunters" without waiting for them to appear; actively participate in the development of, configuring and implementing threat detection analytics.

We will develop the most appropriate protective mechanism for you, corresponding to your specific risk profile.
How to choose a SOC-as-service provider?
When choosing a SOCaaS service provider, check whether they provide:
Pay attention to SLA, for example:
Level 1 – Incident detection and initial notification must be within 1 hour. Ability to receive initial Level 1 notifications.
Level 2 – Checking and notification of incidents within 2 hours. In the case of SOC without authority (monitoring only), the maximum percentage of false positives. In the case of a full-scale SOC, full recovery after the incident within 72 hours.
Level 3 – the number of common indicators of compromise, open sources, proprietary threat analytics sources, Deep Web and Dark Web sources.
- Compliance with the standards and regulatory requirements that your organization must meet (PCI DSS, etc.).
- Storing raw logs for the required period of time.
- Flexibility in the location of SOC and SIEM employees according to your preferences and limitations.
- Security strengthening services (hardening).
- The SIEM platform according to your preferences.
- Multi-tenant management consoles.
- Cyber risk insurance.
Pay attention to SLA, for example:
Level 1 – Incident detection and initial notification must be within 1 hour. Ability to receive initial Level 1 notifications.
Level 2 – Checking and notification of incidents within 2 hours. In the case of SOC without authority (monitoring only), the maximum percentage of false positives. In the case of a full-scale SOC, full recovery after the incident within 72 hours.
Level 3 – the number of common indicators of compromise, open sources, proprietary threat analytics sources, Deep Web and Dark Web sources.
Basic SOC Service
- Monitoring, detection and analysis of potential intrusions in real time and based on historical trends of security data sources.
- Responding to confirmed incidents through security incident (escalation) notifications with information about attacks, threats, vulnerabilities, affected systems and recommendations on how to reduce damage from incidents and vulnerabilities.
- Participate in coordinating resources and taking timely and appropriate countermeasures to respond to incidents.
- Level 1 (Threat response analysts), Level 2 (Incident response engineers) and Level 3 (Domain experts and threat hunters).
- Technologies: FortiSIEM, Kubernetes, Graylog, Elasticsearch, Logstash, Kibana, syslog-ng, Ansible, Splunk, etc.
